Verify JWT issued by Azure Active Directory B2C in Python.
Project description
azure-ad-verify-token
Verify JWT issued by Azure Active Directory B2C in Python 🐍.
Validation steps this library makes:
1. Accepts an Azure AD B2C JWT.
2. Extracts `kid` from unverified headers.
3. Finds `kid` within Azure JWKS.
4. Obtains RSA key from JWK.
5. Calls `jwt.decode` with nessary parameters, which inturn validates:
- Signature
- Expiration
- Audience
- Issuer
- Key
- Algorithm
License
This work is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License.
For commercial use licenses contact us.
Installation
pip install azure-ad-verify-token
Usage
First you'll need to get your azure_ad_app_id, azure_ad_issuer and azure_ad_jwks_uri. See below steps to obtain these.
-
For app id. Login to Azure Portal, navigation to Azure AD B2C, Click on the Applications section and your app id should be listed.
-
For Issuer and JWKS URI:
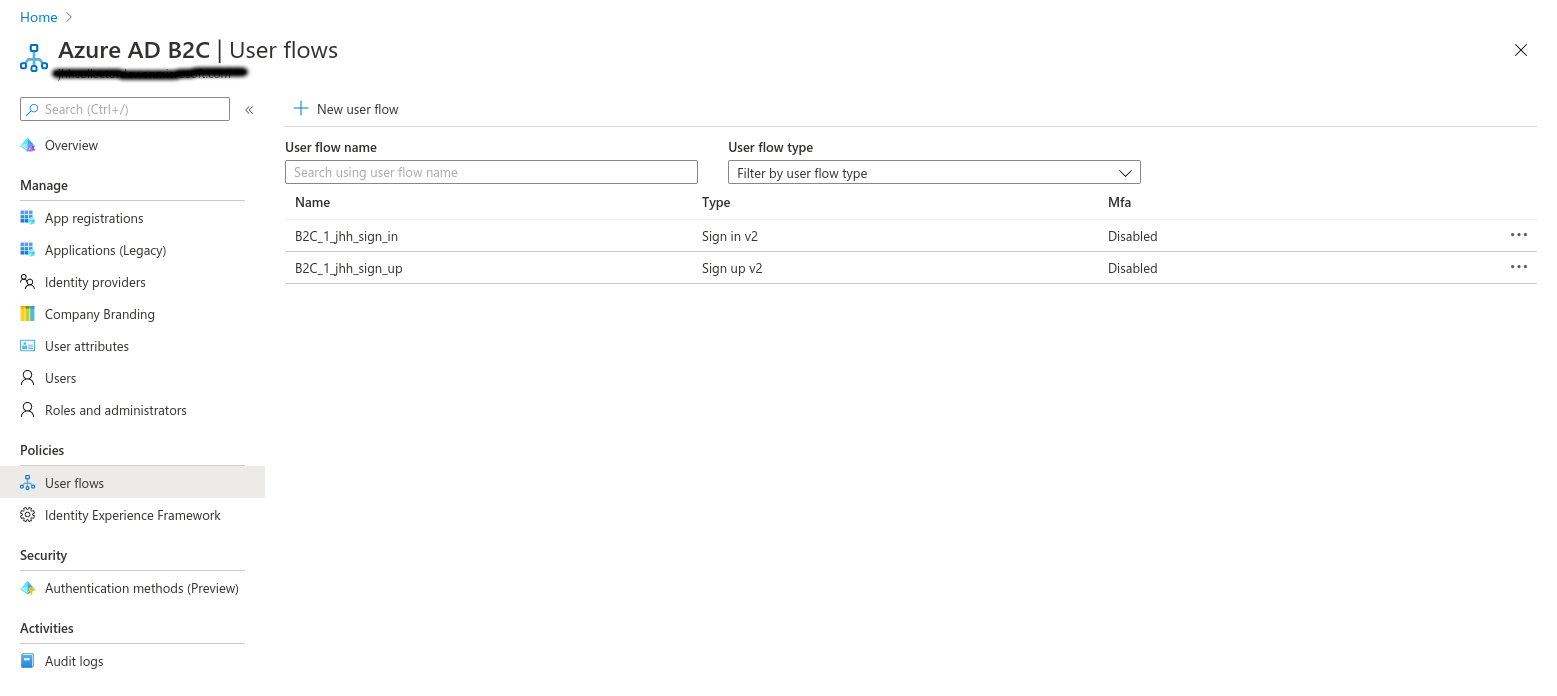
Under the "User Flows", note down the name of yours, this will be needed shortly.
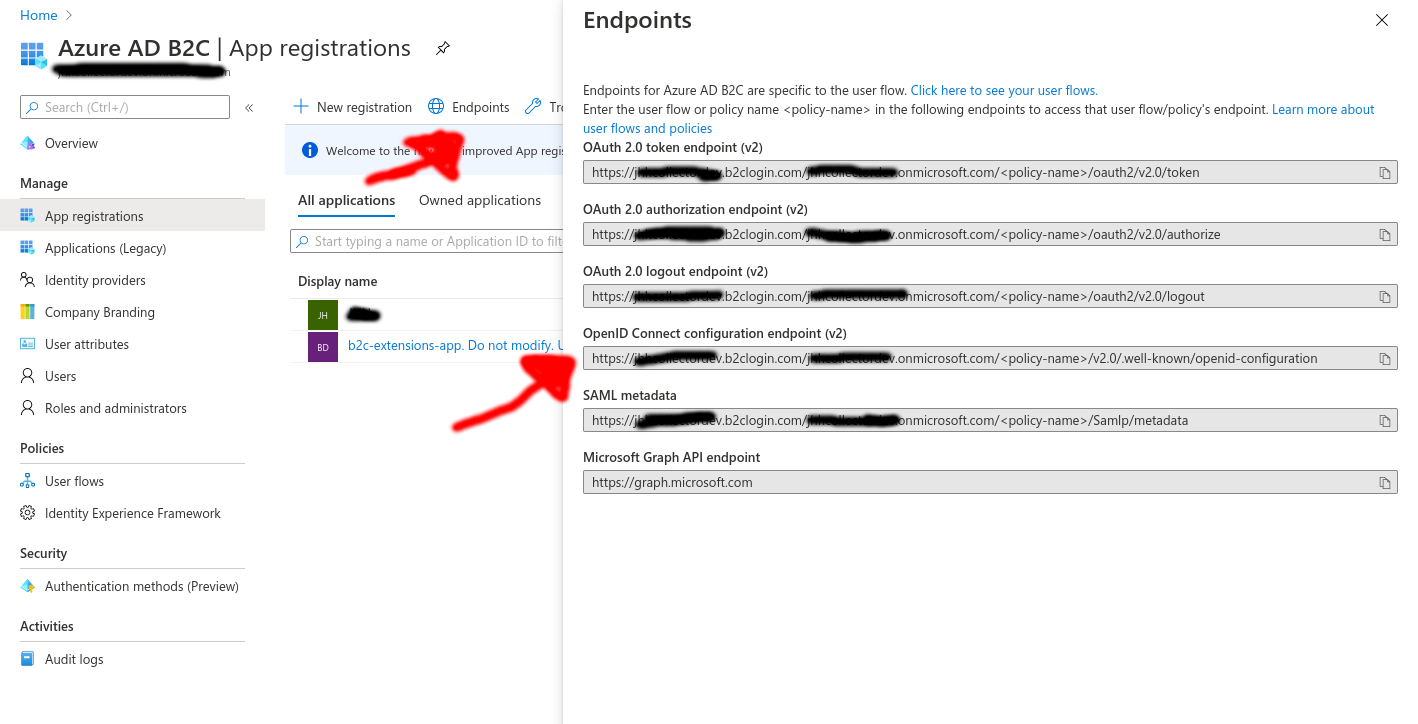
Next, under Azure AD B2C, within the Applications section.
Click on "Endpoints".
Copy the endpoint with the label "OpenID Connect configuration endpoint (v2)"
It will look something like:
https://exampletenant.b2clogin.com/exampletenant.onmicrosoft.com/<policy-name>/v2.0/.well-known/openid-configuration
Now replace <policy-name> with the name of your User Flow from earlier
https://exampletenant.b2clogin.com/exampletenant.onmicrosoft.com/B2C_1_app_sign_in/v2.0/.well-known/openid-configuration
Now visit that URL in your web browser.
You should get a JSON response, note down the values for the keys 'issuer' and 'jwks_uri'.
Now you have those values you can proceed to verify a Azure generated JWT Token.
from azure_ad_verify_token import verify_jwt
azure_ad_app_id = 'b74cd13f-8f79-4c98-b748-7789ecb1111d5'
azure_ad_issuer = 'https://exampletenant.b2clogin.com/0867afa-24e7-40e9-9d27-74bb598zzzzc/v2.0/'
azure_ad_jwks_uri = 'https://exampletenant.b2clogin.com/exampletenant.onmicrosoft.com/B2C_1_app_sign_in/discovery/v2.0/keys'
payload = verify_jwt(
token='<AZURE_JWT_TO_VERIFY_HERE>',
valid_audiences=[azure_ad_app_id],
issuer=azure_ad_issuer,
jwks_uri=azure_ad_jwks_uri,
)
print(payload)
{'aud': 'b74cd13f-8f79-4c98-b748-7789ecb1111d5',
'auth_time': 1591800638,
'emails': ['bob@example.com'],
'exp': 1591804238,
'family_name': 'Exp Admin',
'given_name': 'Richard',
'iat': 1591800638,
'iss': 'https://exampletenant.b2clogin.com/90867afa-24e7-40e9-9d27-74bb598zzzzc/v2.0/',
'nbf': 1591800638,
'sub': 'e07bbc53-b812-4572-9edc-4b5d4ac88447',
'tfp': 'B2C_1_app_sign_in',
'ver': '1.0'}
If something goes wrong, one of the below exceptions will be raised:
# If the token is found to be invalid.
azure_ad_verify_token.InvalidAuthorizationToken
# Base exception, raised if the checks which call the Azure server recieve an unhappy response.
azure_ad_verify_token.AzureVerifyTokenError
Release History
0.1.1 (2020-06-29)
- Documentation updates.
0.1.0 (2020-06-29)
- Initial release.
Project details
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
Source Distribution
Built Distribution
Filter files by name, interpreter, ABI, and platform.
If you're not sure about the file name format, learn more about wheel file names.
Copy a direct link to the current filters
File details
Details for the file azure-ad-verify-token-0.1.1.tar.gz.
File metadata
- Download URL: azure-ad-verify-token-0.1.1.tar.gz
- Upload date:
- Size: 12.6 kB
- Tags: Source
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/3.2.0 pkginfo/1.5.0.1 requests/2.24.0 setuptools/41.2.0 requests-toolbelt/0.9.1 tqdm/4.47.0 CPython/3.8.0
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
6f9d9006662daae331e9e70400201940e3f92fba21ce84d03d656aaf18841d45
|
|
| MD5 |
a0fd288eccca5d830fd2f4bfc186dba3
|
|
| BLAKE2b-256 |
f973a18fa9263938ffccb2ae0030714c2bd24b336e08d28f8756bbd8dd53b0bf
|
File details
Details for the file azure_ad_verify_token-0.1.1-py2.py3-none-any.whl.
File metadata
- Download URL: azure_ad_verify_token-0.1.1-py2.py3-none-any.whl
- Upload date:
- Size: 10.1 kB
- Tags: Python 2, Python 3
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/3.2.0 pkginfo/1.5.0.1 requests/2.24.0 setuptools/41.2.0 requests-toolbelt/0.9.1 tqdm/4.47.0 CPython/3.8.0
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
e94bc919e91259854e83c173d80efc8a6316b455ce56644c5c0d825f490704fc
|
|
| MD5 |
4e2fde3e95ee8ee75ae9e751dd033b80
|
|
| BLAKE2b-256 |
9672a41dfa4482e78432e7238c5ed54609687a0cb1952ae40d91264e86b46d2c
|